Brad McInnis is the founder of cyberzero and the creator of Quantanaut, a cryptographic intelligence platform that helps organizations uncover hidden cryptographic dependencies and plan a practical transition to post quantum security. He has more than twenty-five years of defence intelligence and military experience. In Part 1 of this conversation, Brad unpacks why the overdue migration to Post Quantum Cryptography (PQC) is a necessary response to present day quantum threats and how to overcome the associated governance and cryptographic visibility challenges. In Part 2, Brad frames a quantum defence strategy as the cornerstone of Canada’s ambition to remain a reliable and effective 21stcentury ally.
Canada has participated in at least 14 international military conflicts since World War II. Not once has it fought alone. Every Canadian Defence Policy, including the latest, Our North, Strong and Free (2024), deems Canada’s reliability as an ally as vital to our own security and to our sovereignty.
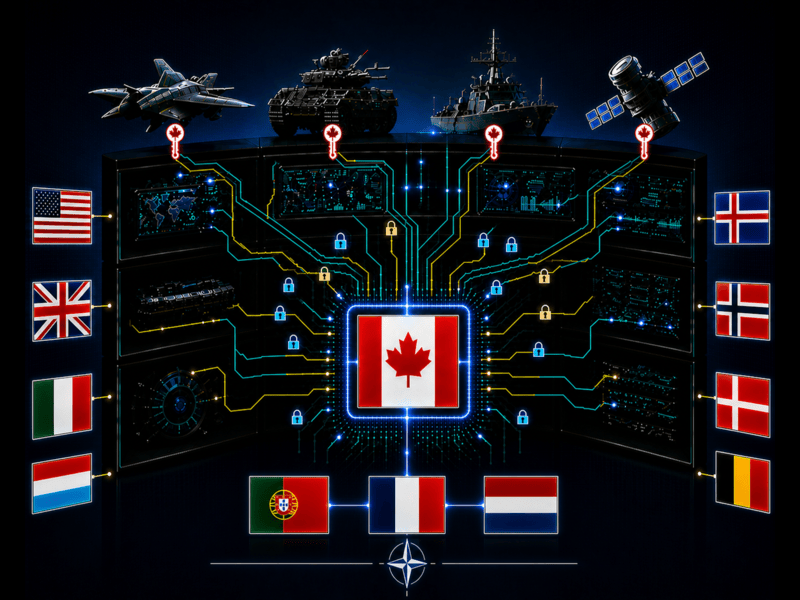
Operational advantages in modern warfare rely on AI/ML analysis of data collected from a network of connected sensors spanning all domains (land, air, sea, space, cyber), so Canada’s reliability as a 21st century ally will effectively depend on interoperability with Allied systems across NORAD, 5 Eyes and NATO.
The Canadian Armed Forces (CAF) conceptualizes this new approach to warfare—which depends on the secure and resilient flow of very large quantities of data—as Pan-Domain Command and Control (PDC2), which it deems essential for Canada to adopt, lest it become an “obsolete” and “irrelevant” ally.
Since PDC2 systems process much greater quantities of data than traditional command and control (C2) systems, the CAF has a choice: secure this data against advances in quantum computing which threaten the security of vital defence communications or forego the multi-domain, real time operational advantages provided by costly PDC2 systems. History is replete with examples of how breaking an adversary’s encryption produced decisive military advantages.
The Government of Canada acknowledged in 2018 that “Canada is the only Five Eyes country without a cloud-first policy,” which impacts “how quickly the GC’s digital vision can be achieved.” If Canada’s path to quantum resilience is paved by the same languid approach to cloud adoption—which has now left Canada behind its Five Eyes allies, who are experimenting with interoperable cloud networks—then Canadian national security will be further undermined at a time when geopolitical risks are increasing.
In Part 1, Brad showed how the present-day quantum computing risks that Canadian enterprises and government departments face makes the transition towards post-quantum cryptography (PQC) standards an integral component of Canadian sovereignty and security.
In Part 2 of this conversation, Brad turns toward the national security imperative for Canada to integrate quantum defences faster than quantum threats evolve. Otherwise, it risks falling behind—and possibly ceding sovereignty to—allies who do.
Why is defence cryptography different than enterprise cybersecurity?
Defence cryptography operates under its own paradigm because “in the enterprise world, the cost of a cryptographic failure is largely measured in dollars, whereas in defence, it can cost lost lives and have national security implications.”
“Cryptography and capability are inseparable in modern military systems,” Brad says. “From the sensors that detect threats, to the datalinks that share targeting information and the logistics systems that sustain operations, modern military platforms depend on cryptography at every layer.”
The complexity of modern military systems stems from their unique operational context that demands functionality in contested electromagnetic environments, across multinational coalitions, on platforms with decades-long lifecycles, and often in locations where you cannot simply push a software update.
It is also immense. Brad believes that “enterprise PQC migrations represent significant challenges, but defence PQC migration is an order of magnitude more complex.”
The fundamentals, however, remain unchanged. PQC migration, either by an enterprise or within a multinational alliance, must be planned and priority-driven to minimize costs and operational disruptions.
What shapes Canada’s approach to defence cryptography?
Over a decade ago, in the United States, the National Security Agency (NSA) had already advised its partners and vendors to plan their PQC migrations. The NSA’s Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) guidance now mandates that all National Security Systems transition to quantum-resistant algorithms by 2035 to secure themselves against the risks posed by a cryptanalytically relevant quantum computer (CRQC).
Canada’s PQC Roadmap aligns with the 2035 timeline. The Roadmap only applies to public sector entities, but once NATO and Five Eyes members collectively acknowledged quantum threats, they also began to prepare their national infrastructure providers for PQC readiness.
This corresponds with the Canadian Centre for Cyber Security’s broader responsibility, which now encompasses Canada’s 10 designated critical infrastructure sectors. Brad is encouraged by the similar structures of responsibility and timelines that exist across the Five Eyes, which will prove crucial for 21st century interoperability between Allied networks, platforms and systems.
How is Canada modernizing its defence cryptography?
Budget 2025 committed more than $81 billion in new defence spending over five years. This generational investment has allowed Canada to meet NATO’s 2% GDP target for the first time and commit to reach the updated 5% target by 2035.
Over $10 billion has been earmarked for the DND/CAF’s and the Communications and Security Establishment’s (CSE) digital infrastructure and cyber capabilities. $334 million is separately allocated to the quantum technology ecosystem, with an additional $900 million over 5 years being invested in quantum and other advanced technologies by the National Research Council under Canada’s recent Defence Industrial Strategy.
Clearly, the funding exists in the aggregate. For Brad, the question is “whether cryptographic modernization is being treated as a first-order priority within that envelope.”
Canada’s Parliament believes it must. A Parliamentary report recently recommended that PQC programs should be “prioritized as a core defence and national security capability.”
If policymakers are serious about prioritizing PQC readiness, a dedicated central funding pool for the government’s PQC migration is an imperative. Without it, Brad does not see how Canada can bridge the gap between policy ambition and implementation posture because a national security driven PQC migration will not succeed if departments have to absorb the corresponding costs within existing IT lifecycle budgets. “This approach works for routine upgrades, but cryptographic modernization is not routine.”
Quantum 2030, the DND/CAF’s Quantum Science and Technology Strategy Implementation Plan announced in 2023, also guides Canada’s development of quantum algorithms for defence and security. It provides a seven-year roadmap with a commitment to develop “prototypes ready to be tested in the field” by 2030. It repeatedly mentions the need for Canada to implement PQC standards that assure “interoperability with allies at all times.”
How will cryptographic requirements and supply chains shape the success of Canada’s defence procurements?
Defence procurement is where policy meets reality. This is why Brad advocates for “embedding cryptographic requirements in procurement from the outset, instead of treating them as a compliance afterthought.”
Canada’s Defence Capabilities Blueprint identifies 13 DCAs (Defence Capability Areas) that are required to operationalize Canada’s PDC2 concept. “Every major defence procurement should include explicit timelines for PQC compliance. Vendors must be contractually obligated to deliver quantum-resistant capabilities, not just promise them.”
The CCCS has published recommended language for cryptographic contract clauses to assist organizations in their PQC migration, which includes requirements for vendors to use CSE-approved algorithms and provide PQC upgrades. “The guidance exists and represents a step in the right direction, but is it being consistently applied across all defence procurements in the absence of explicit PQC requirements in procurement contracts?” Brad asks.
Another layer of complexity is created by the need to align Canadian procurement standards with Allied requirements.
The U.S. Cybersecurity Maturity Model Certification (CMMC) program and the Canadian Program for Cyber Security Certification (CPCSC) evaluate suppliers against different cyber security standards, and mutual recognition between the two programs is not yet feasible. Consequently, “Canadian defence suppliers who work with both countries face the burden of dual compliance, which creates friction and cost that ultimately slows modernization.”
Brad is wary about how this complexity is compounded by ITAR (International Traffic in Arms Regulations) restrictions that place “Canada’s defence industrial base under the dual constraint of aligning with U.S. cryptographic standards for interoperability, while also navigating export control regimes that limit technology transfer and collaboration with non-U.S. allies.”
Vendor lock-in is another concern. Projects that modernize cryptographic infrastructure like the Defence Cryptographic Modernization Project (DCMP) and the Classified Security Management Infrastructure (CSMI) project, which aims to replace legacy Type 1 cryptographic units across the CAF’s inventory, are essential. But, Brad maintains, “they must be designed with cryptographic agility — the ability to adapt to new algorithms as standards evolve — or we will face the same modernization challenge again in 15 years.”
On the F-35 and Embedded Cryptography
“The F-35”, Brad avers, “is perhaps the best example of why defence cryptography demands a different paradigm.” Canada’s Future Fighter Capability Project committed to procuring 88 F-35A Lightning II aircraft, but the F-35 is not just a fighter jet; it is a flying network — a platform where sensors, communications, logistics, and weapons are all integrated through software and bound together by cryptography. A single F-35 can collect approximately 24 terabytes of data across all its 31 onboard sensors and radar systems during a single flight hour.
Consequently, real-time interoperability across Allied C2 systems becomes a crucial component of PDC2, and in late 2024, Project DEIMOS successfully demonstrated the first instance of in-air classified data sharing between F-35 jets involving C2 systems from different nations (U.S. & U.K.).
However, Brad reminds us that “every time an F-35 shares sensor data with another aircraft, authenticates a mission data file, or transmits logistics information, it depends on cryptography for confidentiality, integrity and authentication. If that cryptography is compromised, the platform’s operational advantages erode.”
Significant complexity emerges when ensuring cryptographic security across the aircraft’s Communication, Navigation, and Identification (CNI) suite, its datalinks, including Link 16 (for communication with older aircrafts like the F-16 or F-18) and the Multifunction Advanced Data Link (MADL) (for communication with other F-35s), its Mission Data Files, and its Operational Data Integrated Network (ODIN) logistics information system.
The complexity is compounded by the F-35’s multinational nature that involves over 2,100 suppliers across more than a dozen countries. While cryptographic credential management, software signing, and secure boot chains are all centrally governed in the U.S., the F-35’s Mission Data Files are developed through collaborative reprogramming laboratories like the Australia-Canada-UK Reprogramming Laboratory (ACURL).
Brad is cognizant of the fact that “the question of who controls the cryptographic keys in a multinational weapons platform is not just a technical question; it strikes at the heart of sovereignty because cryptography is the mechanism through which sovereignty is either preserved or surrendered in a connected defence platform.”
With the 2035 PQC migration deadline looming, every cryptographic component of the F-35— from the CNI suite to the ODIN logistics system — will need to be modernized. “That is not a firmware patch”, Brad says, “it is a coordinated multinational cryptographic overhaul across every layer of the platform.”
On Tanks, Sensors, and the Battlefield Network
The F-35 is not unique in its cryptographic dependency. Modern armoured vehicles, sensor networks, and C2 systems are all part of an interconnected battlefield network where cryptography is foundational.
Brad explains: “The anachronistic conception of a tank as armour and a gun differs greatly from today’s tanks which are networked platforms that share targeting data, receive orders digitally, fuse sensor information, and communicate across encrypted channels. If the cryptography fails, modern tanks are isolated.”
Canada’s LAV (Light Armoured Vehicle) 6.0 fleet, for example, incorporates the CP TOPAZ C2 system and communicates through the Iris Digital Communications System across HF, VHF, and UHF bands. “Every vehicle in the fleet depends on cryptographic keys and certificates to participate in the network,” Brad points out. “Managing that across an entire deployed force is an enormous operational challenge.”
Battlefield sensor networks face similar challenges. ISR (Intelligence, Surveillance, Reconnaissance) systems, UAVs, satellite communications, and ground-based sensors all generate and transmit sensitive data that rely on cryptographic material management for secure operations.
Battlefield C2 systems also rely on secure encryption. NORAD’s modernized Cloud Based Command and Control alone ingests over 750 radar feeds and fuses them within a single interface. Canada has separately allocated up to $5 billion for a Modernized Command and Control Information System that is needed to securely leverage data as it transitions from sensors to effectors.
Brad underscores this reality: “The attack surface in modern defence is not limited to a single system. It spans the entire mesh of sensors, platforms, and command nodes — all connected by cryptography.”
On NORAD Modernization and Arctic Sovereignty
Canada has committed $38.6 billion over 20 years to modernize NORAD, including modernized C2 systems, new Over-the-Horizon Radar systems, upgraded sensor networks, enhanced satellite communications, and new northern basing infrastructure.
“NORAD modernization is being built for the next 30 to 40 years,” and Brad cautions that, “if the cryptographic foundations of these systems are not quantum-resilient from the start, we are building infrastructure that will need to be retrofitted before it reaches full operational capability.”
Brad agrees that “the Arctic is Canada’s most strategically important and most cryptographically vulnerable domain.” It presents a unique set of challenges.
Communications above 70°N latitude are unreliable through conventional geostationary satellites. To address this, Canada is investing over $5 billion in the Enhanced Satellite Communications Project – Polar (ESCP-P), which ensures coverage between 65°N – 90°N latitude, but the system is not expected to be operational until 2037. In the interim, the CAF depends on commercial satellite networks with uncertain encryption standards and proven vulnerabilities.
Sensor data from RADARSAT, underwater surveillance arrays, and ground-based radar must also all be transmitted securely, often across vast distances and through challenging environments. “Every link in that chain depends on cryptography and represents a potential target for harvest-now-decrypt-later collection discussed in Part 1.”
On Cyber Warfare and the Threat Landscape
Canada established the Canadian Armed Forces Cyber Command (CAFCYBERCOM) in 2024, with $560 million allocated for its growth. This signals that Canada is taking the cyber domain seriously, but Brad draws a distinction between cyber operations and cryptographic infrastructure: “Cyber operations protect the network. Cryptographic modernization protects the trust that every system on that network depends on. They are complementary but distinct.”
Canada’s 2025-2026 National Cyber Threat Assessment identifies China as the most sophisticated and active state cyber threat facing Canada, while Russia continues to target Canadian government, military, and critical infrastructure as part of ongoing intelligence operations.
The CSE responded to over 2,500 cyber security incidents in 2024-2025 affecting federal institutions and critical infrastructure partners, up from 2,206 in 2020-2021. This averages to nearly 7 incidents per day. The CSE also received 12 Ministerial Authorizations for foreign cyber operations, which reflects the growing offensive dimension of Canada’s cyber posture when compared to the 5 received in 2019-2020.
These trends will likely continue as both China and Russia invest further in cyber capabilities that directly threaten Canadian defence systems. If one of them develops a CRQC first, they have every incentive to closely guard this secret (similar to how the Allies kept secret for over 30 years their ability to break the German Enigma code during WWII).
Quantum and cyber threats are converging, and “the establishment of CAFCYBERCOM is an important step for Canada. But a cyber command without a parallel cryptographic modernization strategy is like building a fortress with a wooden gate. The perimeter looks strong, but the fundamental vulnerability remains,” Brad warns.
How do PQC challenges scale across an alliance like NATO?
NATO countries are at different starting points in their PQC journey. “Agreeing on algorithms is not difficult,” Brad remarks. “While NATO systems are designed to operate across multiple nations, defining a common approach is complicated with 32 countries who have different modernization timelines, security classifications, data naming and labelling practices, and vendors.”
Brad recommends building on NATO’s recent quantum strategy by developing a practical framework that allows members to advance towards quantum readiness at different speeds without undermining coalition security.
“NATO supply chains are also deep and complex,” Brad advises. “They depend on the U.S. defence industrial base, Canadian and UK vendors, and European defence contractors.” Legacy platforms present additional difficulties. Brad caveats that “it may not be possible to upgrade legacy systems to ensure compliance with the latest NIST PQC standards without updating the system itself.”
A NATO PQC framework must therefore address these issues through shared guidance, procurement requirements and coordinated vendor expectations. A ‘replace everything now’ approach will tear asunder the interoperability that is foundational to NATO’s mission and objectives.
Phased modernization, Brad insists, is the only realistic strategy for NATO: “Identify long-lived data, prioritize systems by mission impact, and adopt hybrid cryptography to maintain interoperability while upgrades occur.” “The first technical step is to combine existing classical algorithms (e.g. RSA or ECC) with a post quantum algorithm like ML-KEM or ML-DSA in the same operation.”
This hybrid cryptographic approach is more practical than a wholesale implementation of PQC algorithms across all systems. Security will derive from both sets of algorithms and compatibility with existing systems (e.g. radios and networks) will be preserved amongst partners who are unable to undertake a single ‘big bang’ migration. “Rushing PQC migrations would introduce more risk, not less.”
In closing
Brad recognizes that this is “a critical moment for Canada.”
Canada has a very impressive set of quantum expertise, especially across academia, the defence industry and government. Brad’s own work with cyberzero and the Quantanaut platform serves as an inspiring reminder of what Canadians are capable of at their best, when they think big and risk failure. Brad urges Canada to retain this quantum brain trust because “if the Canadian quantum innovation ecosystem is not cultivated, then that talent will depart.”
Canada needs its quantum talent to overcome the challenges of Canada’s PQC migration and ensure Canada remains an effective and reliable ally in an increasingly unstable geopolitical environment by maximizing the advantages offered by next-generation defence systems.
The Department of National Defence’s 2022/2023 Results Report warned that the CAF was unable to meet all its Arctic and other security objectives because of C4ISR and interoperability related issues. If Canada continues to be hampered by interoperability challenges in the quantum era, Canadian national security will be further undermined at ever greater costs.
Photo: Canada interconnected with its allies (2026), image by Touraj Riazi. Courtesy of the author.
Disclaimer: Any views or opinions expressed in articles are solely those of the authors and do not necessarily represent the views of the NATO Association of Canada.