As artificial intelligence becomes embedded in modern warfare, it is reshaping how states conduct war and raising urgent questions of ethics and accountability regarding the potential absence of human judgment in lethal decisions. If machines can decide when force is used, who ultimately remains accountable for the decision to take a human life in war?
Cyber Security and Emerging Threats
The NAOC’s Cyber Security and Emerging Threats Program features an in-depth analysis of latest trends, developments, and threats in international security. New security concerns are always on the horizon and our program seeks to examine these domains including global warming, natural resources, drones, urban conflicts, and cyberspace.
The program’s mandate is to keep Canadians informed on these rapidly developing and increasingly pivotal realms that are integral to all aspects of security.
Securing the Alliance in the Quantum Era: An Interview with Brad McInnis – Part 2
Brad McInnis is the founder of cyberzero and the creator of Quantanaut, a cryptographic intelligence platform that helps organizations uncover hidden cryptographic dependencies and plan a practical transition to post quantum security. He has more than twenty-five years of defence intelligence and military experience. In Part 1 of this conversation, Brad unpacks why the overdue migration to Post Read More…
Nuclear Allegations and Rhetoric Continue to Undermine Global Peace
Hope Arpa re-evaluates the logic of nuclear deterrence in the context of nuclear programs allegation’s use to justify interventions. The article considers allegations of nuclear programs as motivators of preemptive strikes, discursive tools to justify intervention politically and socially, and the perception of enemy states as nuclear ambitious causing security dilemmas. The root cause of these conflicts is not necessarily framed as exclusively the nuclear weapons themselves, but the international system’s framing of them as the ultimate ‘self-defense’ tools.
Changing the Currents of Conflict: Oil, Water, and the Flows Reshaping the Middle East
Conflict follows the currents of scarcity, and NATO must navigate a world where the most dangerous battles are fought over what no longer flows freely. These behaviours signal a shift in how conflict will unfold: not only through conventional force, but through the manipulation, withholding, and weaponization of essential resources. This article explores three plausible scenarios – oil dominance, water ascendancy, and a dual‑pressure world – to map how resource hoarding could shape the next generation of conflict in the Middle East and beyond, and what this means for NATO’s strategic posture in the decades ahead.
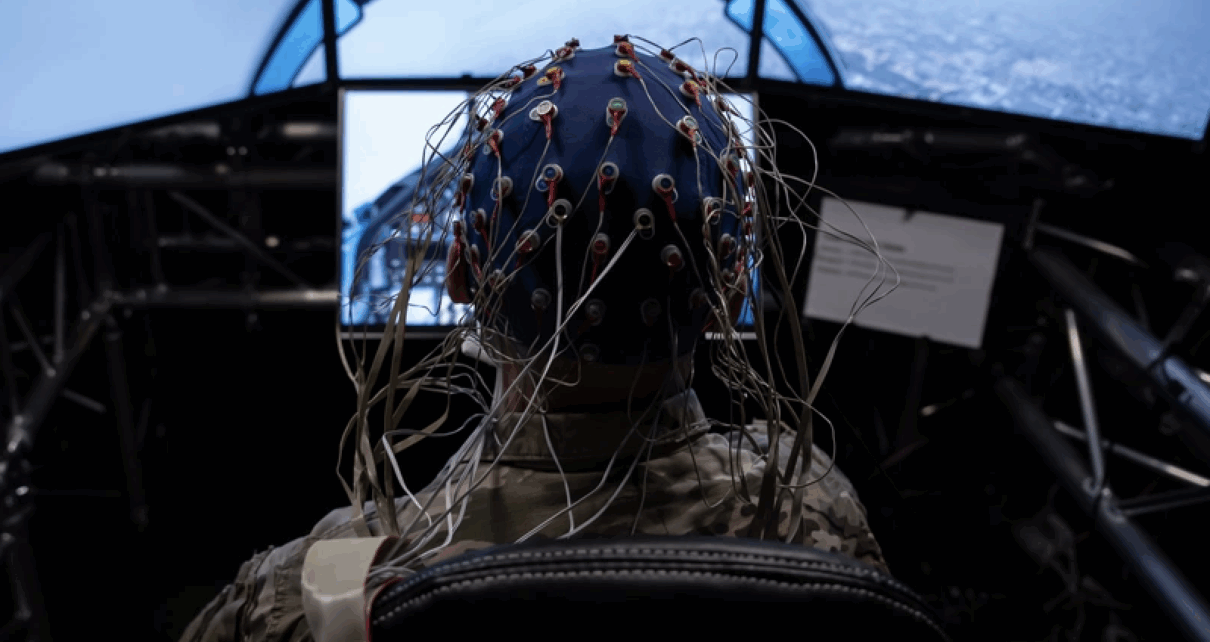
Is NATO Ready for the Brain Battlefield? Navigating the Governance Window for Neurotechnology
In the shadow of artificial intelligence, governments are pouring billions into technologies that collapse the distinction between human thought and machine computation. If NATO does not intervene early, it risks ceding strategic influence to competitors who view the mind as a domain for military advantage. Yet the strategic promise of neurotechnology is matched by questions about control, accountability, and exploitation that the Alliance cannot afford to ignore. NATO must move quickly, but through a phased approach that balances innovation with the protection of cognitive integrity.
Les algorithmes au pouvoir : comment l’IA redéfinit la guerre de l’information?
Dans l’espace numérique, l’information circule à une vitesse inédite. Les réseaux sociaux permettent à chacun de diffuser des contenus en quelques secondes auprès d’un public mondial, favorisant les échanges d’idées à grande échelle. Pourtant, ils facilitent aussi la propagation de contenus trompeurs. Avec l’essor de l’intelligence artificielle (IA), cette réalité a franchi un nouveau cap Read More…
Protecting Arctic Cyberinfrastructure: Quantum Sensors for Domain Awareness in the North
This article discusses how the adoption of quantum sensing technologies will likely advance cybersecurity by enabling greater protection of infrastructure, detection of attacks, and attribution to attackers, particularly in the Arctic.
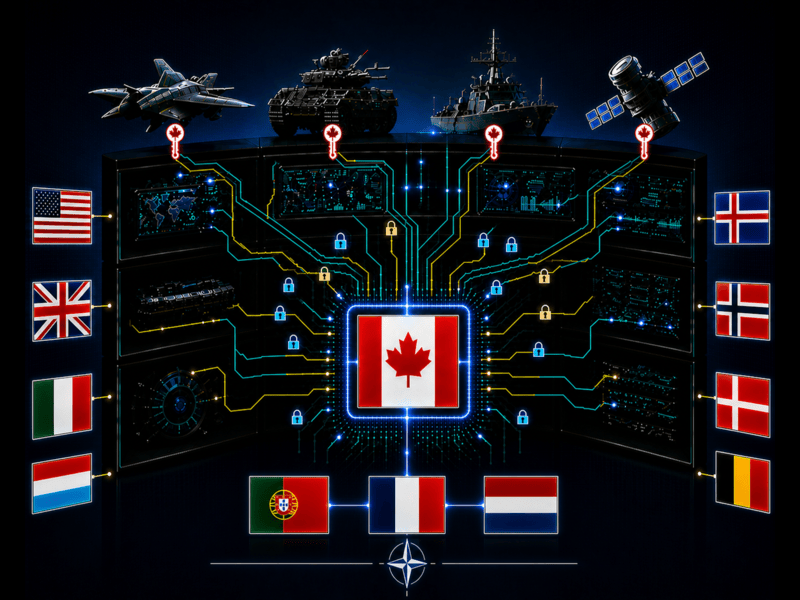
The Missing Shield: Why NATO’s Innovation Strategy Needs Modern Intellectual Property Protection
This article argues that without integrating IP protection into its cyber, emerging and disruptive technologies, and innovation strategies, NATO risks undermining the very technological edge it seeks to secure.
Canada’s Arctic Surveillance at Risk, Are Space Capabilities Enough to Defend Sovereignty?
The Arctic, a remote and expansive region, is heavily reliant on satellite surveillance to maintain domain awareness. As climate change accelerates, increased access to the region, along with its growing strategic and economic value, has drawn heightened interest from states such as Russia and China. The interests and activities of these actors raise security concerns Read More…
Canada Already Entered the Quantum Era: Is it Exposed or Ready for What Comes Next?
An Interview with Brad McInnis Part 1 Brad McInnis is a cybersecurity and cryptographic resilience expert with more than twenty-five years of experience spanning industry, Canadian defence intelligence, the Five Eyes community, U.S. government and defence environments. His work has focused on long term confidentiality, enterprise key management, and large-scale cryptographic modernization for national level systems. He Read More…